If you’re looking at Ethical Hacking, you’re looking at one of the most in-demand, highest-paying, and future-proof careers in the Nigerian job market for 2025.
You see the headlines: Flutterwave experienced a security breach, FinTech startups need specialists, and new regulations like the NDPR are driving a massive demand for defenders.
This isn’t just a trend; it’s a critical shortage of skilled professionals.
But where do you start? The field is complex, there are lots of unfriendly jargons, and the online guides are overwhelming.
This article is your definitive roadmap that gives you clear, actionable answers based on Nigerian market realities: what the job really is, how much you can realistically earn in Naira, and a step-by-step plan to get your first specialized role.
Let’s begin by defining your new career.
What Exactly Is Ethical Hacking?
Ethical Hacking (also known as Penetration Testing or Pen Testing) is the authorized, legal attempt to gain access to a computer system, application, or network.
Your goal is not theft or malice. It is to simulate a real cyberattack to find and exploit security vulnerabilities before a malicious hacker (a “Black Hat”) can.
The Non-Negotiable Protocol and Limitations
Ethical hacking is governed by a strict, mandatory code of conduct (Cybercrimes Act, NDPR):
- Stay Legal (Permission First): You must have explicit, written permission from the organization or asset owner before touching any system. No permission, no hacking.
- Define the Scope: You must agree on a defined scope; what systems you can test and what techniques are off-limits.
- Report Everything: You must document and disclose all vulnerabilities discovered to the organization and provide remediation advice.
Why Ethical Hacking is the Most In-Demand Career in Nigeria
The demand is driven by two key forces:
- Compliance: Mandatory regulations like the Nigeria Data Protection Regulation (NDPR) require organizations to conduct frequent security audits and risk assessments, creating a continuous need for ethical hacking services.
- Investment: Aggressive VC funding in FinTech means high-value assets are constantly at risk, driving companies to hire specialists who can secure their platforms before launch.
Types of Hackers
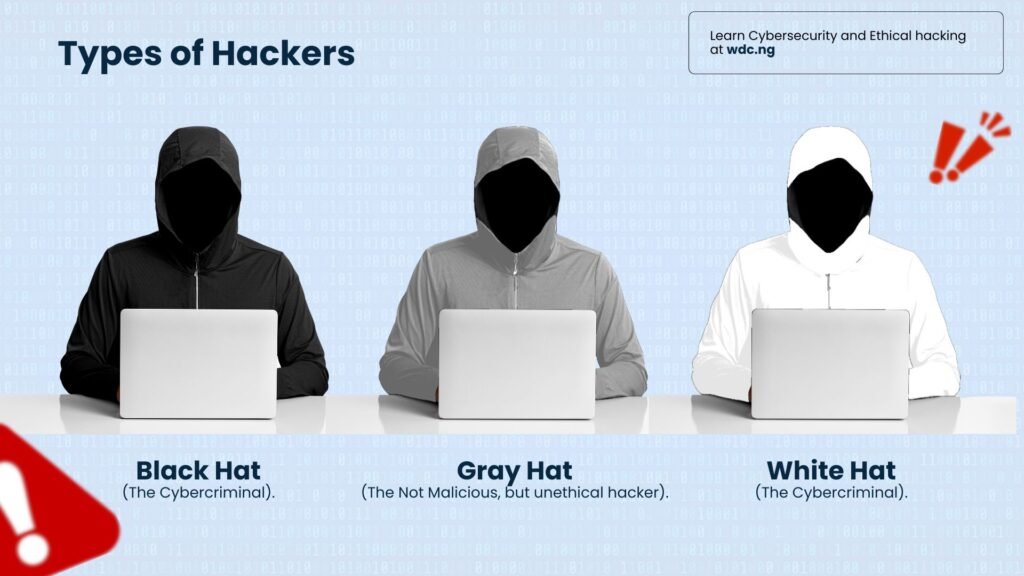
Understanding the different “hats” is crucial, as only one is a viable, high-paying career path.
| Category | Role / Motivation | Legal Status & Career Path |
| ⚪ White Hat Hacker | The Ethical Defender. Works legally, with permission, to secure and improve systems. Motivation:Professional fees, job security, and defense. | Legal & Professional. This is the role of a Penetration Tester, SOC Analyst, or Security Consultant. This is your goal. |
| ⚫ Black Hat Hacker | The Cybercriminal. Exploits systems for financial gain, data theft, or sabotage. Motivation: Profit, personal gain, or malice. | Illegal & High-Risk. Violates the Nigerian Cybercrimes Act and leads to criminal prosecution. |
| ⚫⚪ Gray Hat Hacker | Operates without permission, often exposing a vulnerability publicly to “shame” the company into fixing it. Motivation: Ego, or a misguided sense of public good. | Unethical & Illegal. Even with good intentions, hacking without permission is illegal and will destroy your professional career. |
The Takeaway: If you want a long, secure, and highly compensated career, your focus must be 100% on White Hat ethical practice.
The Core Methodology & Scope
The Five Phases of Hacking
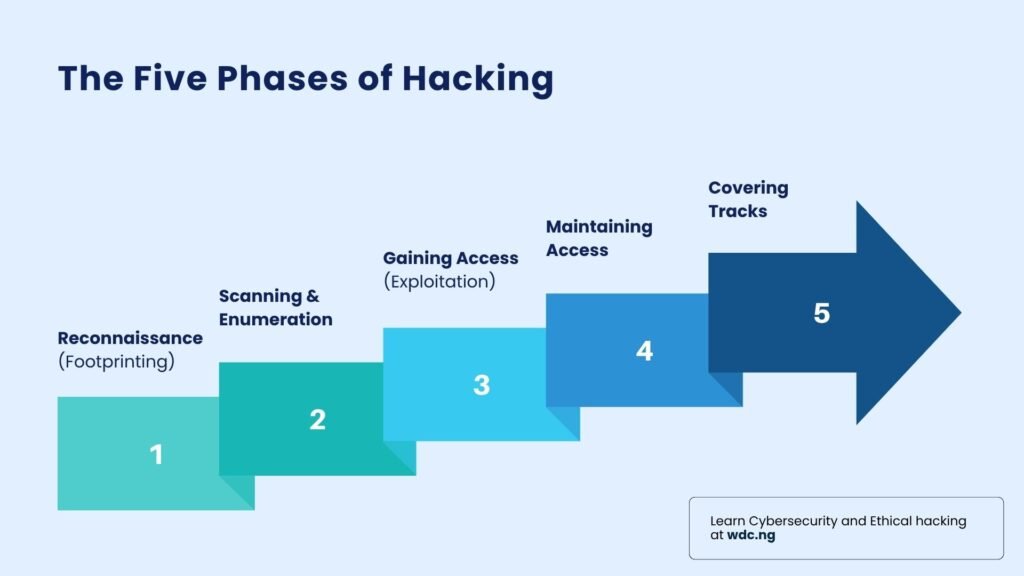
When a pro starts a Pen Test, they don’t just randomly start typing. They follow a clear, systematic process, like a detective following clues. This process ensures thoroughness:
- Reconnaissance (Footprinting): This is the quiet planning phase. You gather all possible information about the target from public sources (social media, corporate websites) before making any direct contact. It’s all about scouting the territory.
- Scanning and Enumeration: Now, you start poking. You use tools like Nmap to see which ports are open, which services are running, and where the potential entry points are. You are mapping the digital weak spots.
- Gaining Access (Exploitation): This is the moment of truth. You use specialized exploits or techniques to bypass security and enter the system. You’re inside the gates.
- Maintaining Access: Once inside, you assess the damage. You might try to install a hidden backdoor to ensure you can re-enter later, checking if the client’s monitoring systems detect you.
- Covering Tracks (Reporting is Key): You delete log files to mimic a covert exit, and then—most importantly—you write the professional report detailing exactly how you got in and, crucial, how they must fix it.
What Ethical Hackers Hunt For
You’re not looking randomly; you are a specialist hunter. You focus on established weaknesses:
- Web Application Vulnerabilities (The OWASP Top 10): Most security flaws are in the client’s website or mobile app APIs. You hunt for issues like SQL Injection (tricking the database) or Broken Authentication (bypassing login).
- Network and Infrastructure Flaws: You check for simple things like default passwords, exposed ports, or unpatched software running on critical servers. Sometimes the simplest oversight is the biggest flaw!
- The Human Element (Social Engineering): You assess how easy it is to trick employees into giving up information, often using phishing or, in 2026, AI-powered deepfakes to impersonate executives.
Ethical Hacking Salary in Nigeria: What You Can Expect in 2025 and Beyond
The high demand and the limited number of ethical hackers in Nigeria translates directly into competitive salaries that reward specialization.
Here are the realistic ranges for 2025, based on local market reports and job aggregator data:
| Experience Level | Typical Annual Salary Range (₦) | What Moves the Pay |
| Entry-Level (0-2 Yrs) | ₦1.2 Million – ₦3.0 Million | Mandatory Certifications (Security+, CEH) and hands-on portfolio experience. Most common roles: SOC Analyst, Junior Security Analyst. |
| Mid-Level (3-5 Yrs) | ₦4.5 Million – ₦9.0 Million | Advanced Certifications (OSCP, CISSP), deep expertise in one domain (e.g., Cloud Security or Web App Pen Testing). |
| Senior/Leadership | ₦12 Million – ₦50 Million+ | Roles like Security Architect, Head of InfoSec, or CISO (Chief Information Security Officer) command the highest salaries in large banks and multinationals. |
The High Earning Path: The fastest way to break the local salary ceiling is through remote, USD-denominated contracts, which are only achievable if you hold advanced, globally recognized certifications and a powerful, verifiable portfolio of real-world experience.
How to Get Started (The Ethical Hacking Learning Path)
‘I now understand what ethical hacking is about, the scope and salary potential. But Joshua, can you give me a simple step-by-step structure to acquiring this skill?’
Sure. Here’s the summary of full, proven, step-by-step guide on how to start a successful career in Ethical Hacking
Step 1: Understand the Foundation (The Non-Negotiables)
You cannot secure a system (or break it) until you understand how it works. Your first priority should be mastering the core technology that underpins all cybersecurity.
- Core Focus: Mastery of Networking (TCP/IP and the OSI Model) and Operating Systems (Linux Command Line).
- The Goal: Fluency in the languages and protocols that govern digital communication.
Step 2: Get Certified Strategically (Validation)
Once you have the knowledge, you must prove it. Certifications are the currency in the Nigerian job market that gets your resume past HR filters.
- Core Focus: Strategic preparation for industry-recognized certifications like CompTIA Security+, CEH, or Certified SOC Analyst (CSA).
- The Goal: Acquire the validated proof of your skills required for entry-level roles (e.g., SOC Analyst)..
Step 3: Build a Portfolio (The Experience Bridge)
The critical step is translating knowledge into demonstrable, hirable experience. Employers pay for what you can do, not just what you know.
- Core Focus: Hands-on practice in safe labs, participation in CTF (Capture The Flag) challenges, and mastering the professional art of vulnerability reporting.
- The Goal: Build a portfolio of documented projects that directly solve the “no experience” paradox.
Step 4: Network and Go Advanced
Once you have a strong portfolio, connect with local Security Analysts and Pen Testers in the Fintech and Banking space.
The WDC Ethical Hacking Program: Your Unique Advantage
The truth is,
Becoming a successful penetration tester requires more than reading books, watching YouTube videos, and taking some online courses.
Over the years, we’ve seen the importance of mentor-led practice; having a professional to guide you. It is fast and effective
The Wildfusion Digital Centre (WDC) Ethical Hacking Program is your complete execution engine. We bypass the risk of self-study by providing the structured system required to master the roadmap:
- A Structured Curriculum: Learning the skills in the absolute right order.
- Mentor-Led Experience: Getting critical feedback while building your portfolio.
- Efficiency: Avoiding the rabbit holes that waste time and money.
- Guaranteed Certifications: We prepare you for the EC-Council certifications that serve as the mandatory validation required by the local industry.
Frequently Asked Questions (FAQs)
- Is Ethical Hacking legal in Nigeria? Yes, absolutely. It is a legal, professional service. However, you must always have explicit, written permission to test any system.
- How long will it take me to become job-ready? With intensive, structured training focusing on hands-on labs and certification prep (like the WDC program), you can become job-ready in 3 to 6 months.
- Which certification is the best to start with? CompTIA Security+ is the best entry-level choice to prove foundational knowledge. The Certified Ethical Hacker (CEH) is highly requested in local Nigerian job postings for specialization.
- Can I earn money from Bug Bounties in Nigeria? Yes. Bug bounty platforms are global. Earning requires advanced skills and dedicated effort, but it is a legitimate source of income and excellent portfolio material.
If you are serious about building your successful career then it’s time to explore a structured path.
Don’t wait months to find the right guide. Start today.




